Rewriting the News Is Not Intelligence — But Someone Still Has to Do It.
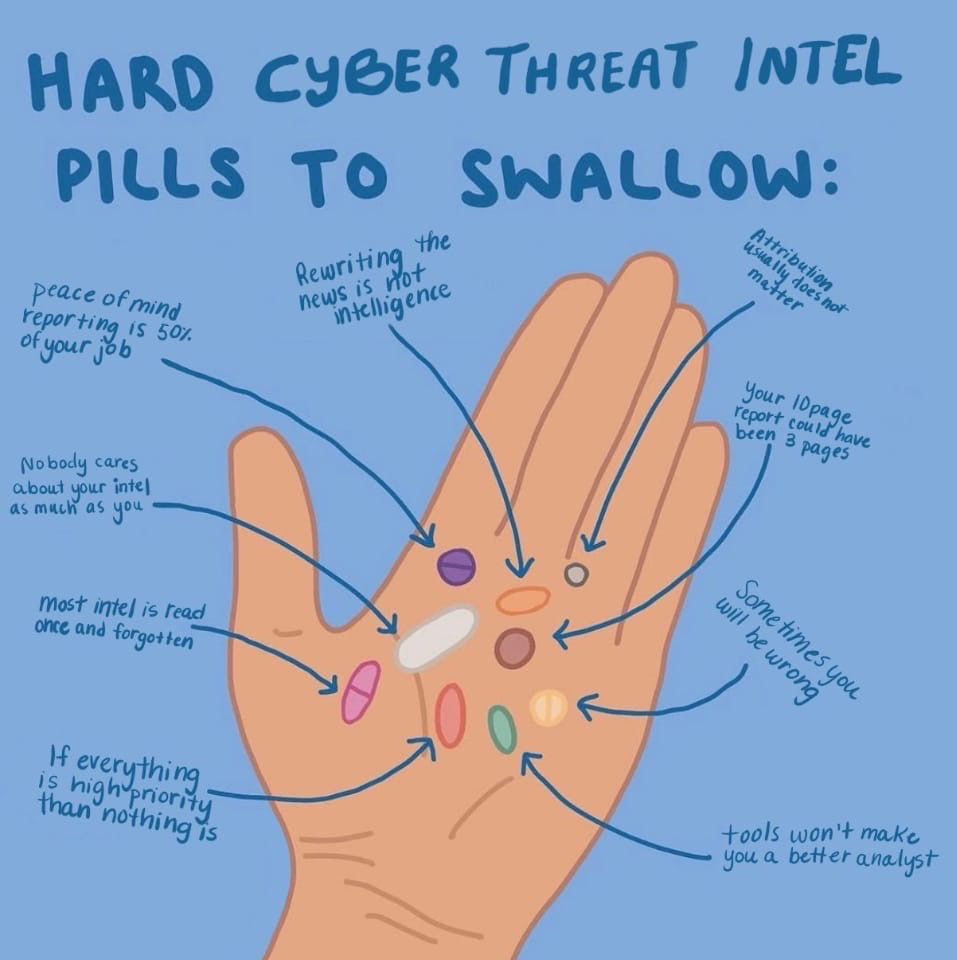
There's an image making the rounds in the CTI community right now. You've probably seen it — white text on a dark background, listing nine “Hard Cyber Threat Intel Pills to Swallow.” It's the kind of thing that gets screenshot-shared into every threat intel Slack channel and group chat within about forty-eight hours.
And I get why. Because most of these pills? They sting a little. Some of them sting a lot. They sting because they're largely true.
But “largely true” is doing a lot of heavy lifting in that sentence. A few of these deserve a more honest conversation than a meme format allows. So let's have that conversation. (If you want the fuller picture of what CTI actually is before we pick the meme apart, start with a practitioner's guide to the intelligence lifecycle.)
The pills that are just... correct
Let me get the easy ones out of the way first.
“If everything is high priority then nothing is.” Yes. Full stop. I've worked with CTI teams at every maturity level, and this is the single most common failure mode I've seen. When every report is tagged critical, you haven't prioritised — you've just created a pile. Your stakeholders learn to ignore the labels, and eventually they learn to ignore you. Prioritisation isn't about finding threats. It's about having the courage to say “this one matters more than that one” and standing behind it.
“Your 10 page report could have been 3 pages.” Also correct, and I say this as someone who has written many reports that could have been shorter. The instinct to be thorough is understandable — nobody wants to be the analyst who left out the one detail that mattered. But thoroughness and length are not the same thing. The best intelligence product I ever received was a single paragraph with three bullet points underneath it. Told me exactly what changed, why it mattered to us, and what to do about it. I still remember it. I cannot say the same about any ten-page report I've ever read.
“Sometimes you will be wrong.”If you haven't been wrong yet, you haven't been doing this long enough. The question isn't whether you'll get it wrong — it's whether your organisation has the maturity to treat that as a data point rather than a career event. I've made calls that turned out to be wrong. The teams I respected most were the ones where we could talk about that openly and adjust, rather than pretending it didn't happen.
The pills that need more nuance
“Nobody cares about your intel as much as you.” This one's true, but framing it as a pill to swallow implies it's a problem with your stakeholders. It's not. It's the natural state of things. A SOC analyst cares about their alerts. A vulnerability manager cares about their patching queue. Your intelligence is an input to their work, not their entire world. That's healthy. The real pill to swallow is that it's your job to make your intelligence impossible to ignore — not their job to come find it and be grateful.
“Attribution usually doesn't matter.” I spent years in law enforcement, including time at Europol's Joint Cybercrime Action Taskforce. In that context, attribution is literally the point. But in a corporate security context? For most organisations, most of the time, this pill is right. Knowing that APT-whatever hit you is interesting. Knowing what TTPs they used and whether your detections cover them is useful. If you're spending more time on the “who” than the “so what,” you've lost the plot. The exceptions are real — some sectors and some threat scenarios genuinely require attribution. But those teams usually know who they are.
“Tools won't make you a better analyst.” True in the same way that “a better guitar won't make you a better musician” is true. Technically correct, widely misunderstood. No, tools won't compensate for bad analytical thinking. But the right tools, in the hands of a competent analyst, remove the friction that prevents them from doing their best work. The problem in CTI has never been a shortage of smart people. It's that those smart people spend 80% of their time on tasks that don't require their intelligence at all.
Which brings me to the pill I want to spend real time on.
“Rewriting the news is not intelligence”
This is the one that got the strongest reaction in my feed, and I think it's because it's simultaneously the most true and the most unfair pill on the list.
Let me explain what I mean.
The part that's true
If your entire CTI function consists of reading security news, summarising it, and emailing it to stakeholders — that is not intelligence. It's media monitoring with a cybersecurity label on it. Intelligence requires analysis: context, assessment, relevance to your specific organisation, a judgment call about what it means and what to do about it. A summary of what Krebs or The Record published this morning is not that.
The people who made this meme are not wrong about this. I've seen CTI teams whose entire output is effectively a curated RSS feed dressed up in a report template. That's not a good use of trained analysts, and it's not what the intelligence lifecycle describes.
The part that's unfair
Here's where I push back: the monitoring and reporting work still needs to happen. Someone in the organisation needs to be watching the landscape, tracking what's being published, filtering for relevance, and making sure stakeholders are informed about breaking developments. That work is real, it's necessary, and it's crushing.
A mid-market organisation — say, 2,000 to 10,000 employees — typically has a CTI team of one to three people. Maybe less. Those analysts are responsible for everything: strategic assessments, tactical reporting, indicator management, stakeholder briefings, vendor liaison, and yes — monitoring the news and making sense of it for the rest of the security function. Every morning, they wake up to hundreds of new articles, vendor advisories, vulnerability disclosures, and social media posts. They have to filter all of that down to what matters.
I've worked with teams exactly like this. At Barclays, at Mandiant, advising government teams in the Middle East. The pattern is always the same: the team knows they should be doing more strategic work, more threat hunting, more proactive analysis. But the daily grind of collection, monitoring, and reporting eats every available hour. By the time they've processed the morning's intake and pushed out the daily summary, the day is half gone.
When someone says “rewriting the news is not intelligence,” I want to ask: when exactly should these analysts be doing the intelligence part? Before 7 AM? After midnight?
The real problem this pill points to
The meme isn't wrong that something is broken. It's just pointing at the wrong thing. The problem isn't that analysts are doing monitoring and reporting work. The problem is that the monitoring and reporting work is so time-consuming that it crowds out everything else. The collection and dissemination phases of the intelligence lifecycle are eating the analysis phase alive.
This is a structural problem, not a skills problem. You don't solve it by telling analysts to “do better intelligence.” You solve it by making the collection and reporting work take less time.
What changes when AI handles the grind
This is where I'll be transparent about my bias: I founded Liberty91 specifically because I saw this problem destroy team after team. Smart analysts, doing rote monitoring work, burning out, producing mediocre output because they never had time for the work they were actually trained to do.
AI — and I mean purpose-built AI for threat intelligence, not a ChatGPT prompt — changes this equation fundamentally. Not because it replaces analysts. It doesn't. It handles the parts of the job that don't require human judgment.
Collection across hundreds of sources, in real-time, 24/7? That's a compute problem, not an intelligence problem. Filtering for organisational relevance based on your sector, your tech stack, your threat profile? That's pattern matching — exactly what machine learning is built for. Structuring raw information into a report format with IOCs, affected assets, and detection rules? That's templated synthesis, and AI does it faster and more consistently than any human.
What AI doesn't do well is assess intent. It doesn't read between the lines of a threat actor's operational tempo. It doesn't sit in a room with your CISO and explain why this quarter's threat landscape means the security roadmap needs to shift. It doesn't build relationships with peer organisations to share intelligence informally. It doesn't develop hypotheses and hunt for evidence.
Those are the things your analysts were hired to do. Those are the things they're not doing because they're too busy rewriting the news.
At Liberty91, we built our platform around exactly this division of labour. Our AI agents handle the collection, monitoring, filtering, and reporting — the 80% of the cycle that's necessary but doesn't require a trained analyst's brain. The result isn't less intelligence. It's more intelligence, because the human analysts finally have time to do the analytical work that no AI can replace.
The pill that should have been on the list
If I were adding a tenth pill, it would be this: “Your analysts are doing work that doesn't need a human, and that's your fault, not theirs.”
Most CTI teams aren't underperforming because they lack skill. They're underperforming because the operational overhead is impossible. You've hired smart people and buried them in admin. You wouldn't hire a detective and then have them spend all day filing paperwork — but that's essentially what we do to threat intelligence analysts.
The “hard pills” meme resonates because everyone in CTI recognises these patterns. But the answer isn't to shame analysts for the state of their output. The answer is to fix the structural problem that makes quality output impossible.
What to do about it
If you're a CTI team lead or a CISO reading this, and some of these pills hit uncomfortably close to home, here's my honest advice:
Audit where your team's time actually goes.Not where you think it goes — where it actually goes. Track it for two weeks. I'd bet money that collection, monitoring, and report formatting eat 60-80% of productive hours. That's the 80/20 problem in cyber threat intelligence, and it's solvable.
Stop measuring output by volume.Ten reports nobody reads is worse than two reports that change behaviour. If your KPI is “number of reports produced,” you're incentivising exactly the wrong thing.
Automate the bottom of the stack. Whether it's Liberty91or another approach, get the rote collection and reporting work off your analysts' plates. The technology exists now to do this well. There's no reason a trained intelligence professional should be manually checking vendor blogs every morning.
Give your analysts permission to analyse.This sounds obvious, but it's not. Many teams have been in reactive mode for so long that they don't know what proactive intelligence work looks like anymore. Create space for it. Protect it. The strategic value of your CTI programme lives there.
Swallowing the pills
The “Hard CTI Pills” image is having a moment because it names things that most people in this field have been thinking quietly for years. That takes guts, and the community is better for the conversation.
But memes are blunt instruments. The reality behind most of these pills is more nuanced than “swallow it and move on.” The real hard pill is that we've built an industry where talented analysts spend most of their time on work that a machine could do better and faster — and then we wonder why the intelligence output doesn't meet expectations.
That's the pill I'm trying to help the industry swallow. And it's the reason Liberty91 exists.


